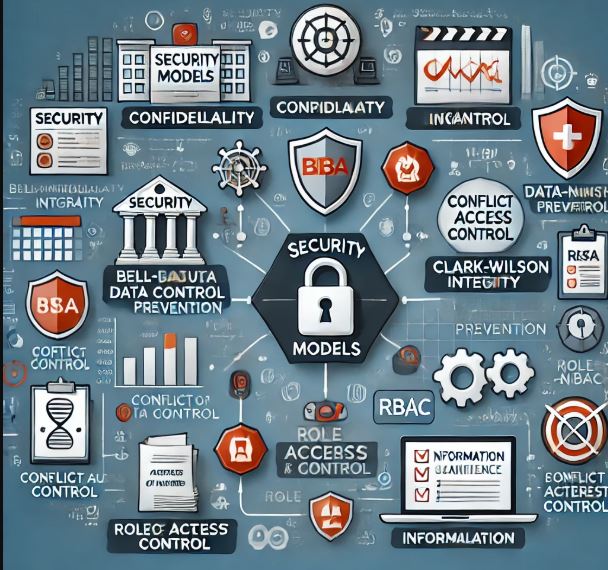
1. CIA Triad (Confidentiality, Integrity, Availability)
The CIA triad ensures that security measures align with core protection goals.
- Confidentiality: Prevents unauthorized access to data.
- Encryption, access controls, data masking, and user authentication.
- Example: Encrypting customer records in a database.
- Integrity: Ensures data accuracy and prevents unauthorized modifications.
- Hashing, checksums, digital signatures, and version controls.
- Example: Implementing file integrity monitoring (FIM) to detect changes in sensitive files.
- Availability: Ensures resources and data are accessible when needed.
- Redundancy, failover solutions, DDoS protection, and backups.
- Example: Deploying a high-availability (HA) architecture for critical applications.
Designing a Security Policy
- Define data classification levels (public, confidential, restricted).
- Implement role-based access control (RBAC).
- Specify disaster recovery and incident response measures.
Deploying a Security Solution
- Configure firewalls, IDS/IPS, and endpoint protection.
- Implement encryption and data integrity checks.
- Set up redundant systems and monitoring tools.
2. DAD Model (Disclosure, Alteration, Destruction)
DAD represents security threats that counteract the CIA principles.
- Disclosure (Threat to Confidentiality): Unauthorized exposure of sensitive data.
- Countermeasures: Encryption, access control lists (ACLs), VPNs.
- Alteration (Threat to Integrity): Unauthorized modification of data.
- Countermeasures: Digital signatures, hashing, integrity monitoring.
- Destruction (Threat to Availability): Data loss or system failure.
- Countermeasures: Regular backups, disaster recovery plans, redundancy.
Security Policy Design
- Define measures to mitigate each threat category.
- Conduct regular risk assessments and vulnerability scans.
- Implement data retention and destruction policies.
Security Solution Deployment
- Apply least privilege access to limit exposure.
- Monitor and log system changes.
- Use robust backup and recovery strategies.
3. AAA Framework (Authentication, Authorization, Accounting)
AAA provides access control and accountability for systems.
- Authentication: Verifies user identities.
- Passwords, multi-factor authentication (MFA), biometrics.
- Example: Requiring employees to log in using MFA before accessing systems.
- Authorization: Defines user permissions and access levels.
- Role-based access control (RBAC), least privilege principle.
- Example: Limiting access to HR data only to HR personnel.
- Accounting: Tracks user activities for auditing and compliance.
- Logging, session tracking, audit trails.
- Example: Monitoring and logging administrator actions on critical systems.
Security Policy Design
- Define authentication and access control mechanisms.
- Set up logging and monitoring requirements for compliance.
- Enforce least privilege and need-to-know principles.
Security Solution Deployment
- Implement Identity and Access Management (IAM) systems.
- Enforce logging and monitoring of user activities.
- Configure automated alerts for suspicious activities.
Bringing It All Together
- Use CIA to define security objectives.
- Identify threats using DAD and mitigate them.
- Apply AAA to enforce access controls and accountability.