-

Change Management & Security: Why It’s Critical for Cyber Resilience
Change management plays a crucial role in improving security by providing structured processes to manage, monitor, and mitigate risks associated…
-

𝗧𝗵𝗲 𝘁𝗼𝗽 𝗺𝗼𝘀𝘁 𝘂𝘀𝗲𝗳𝘂𝗹 𝗰𝘆𝗯𝗲𝗿𝘀𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝗹𝗮𝘄𝘀:
𝟭. 𝗚𝗲𝗻𝗲𝗿𝗮𝗹 𝗗𝗮𝘁𝗮 𝗣𝗿𝗼𝘁𝗲𝗰𝘁𝗶𝗼𝗻 𝗥𝗲𝗴𝘂𝗹𝗮𝘁𝗶𝗼𝗻 (𝗚𝗗𝗣𝗥) – 𝗘𝘂𝗿𝗼𝗽𝗲 📌 Why It’s Useful: One of the strongest data protection laws. Protects…
-

𝗛𝗼𝘄 𝗔𝗰𝗾𝘂𝗶𝘀𝗶𝘁𝗶𝗼𝗻𝘀, 𝗠𝗲𝗿𝗴𝗲r𝘀, 𝗮𝗻𝗱 𝗗𝗶𝘃𝗲𝘀𝘁𝗶𝘁𝘂𝗿𝗲𝘀 𝗜𝗻𝗰𝗿𝗲𝗮𝘀𝗲 𝗢𝗿𝗴𝗮𝗻𝗶𝘇𝗮𝘁𝗶𝗼𝗻𝗮𝗹 𝗥𝗶𝘀𝗸
Mergers, acquisitions, and divestitures can transform businesses, but they also introduce significant risks—from cybersecurity threats to operational disruptions. Here’s why…
-
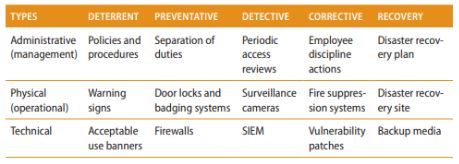
Types and Purpose of Security Controls
Security controls are measures designed to protect the confidentiality, integrity, and availability (CIA Triad) of systems and data. These controls…
-
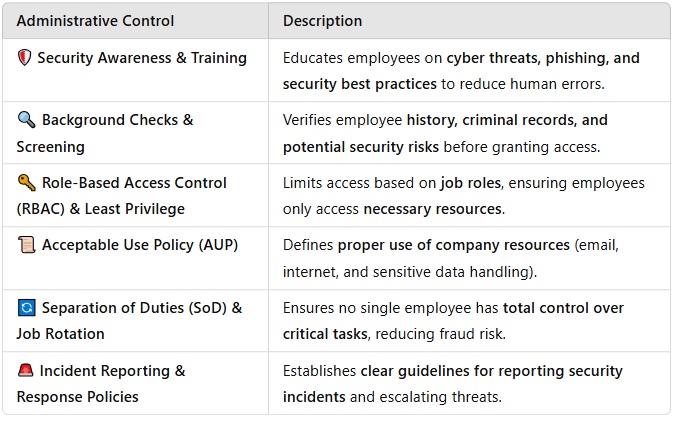
Six Administrative Controls to Secure Personnel
Administrative controls are policies, procedures, and practices designed to manage personnel security risks in cybersecurity. These controls ensure that employees…
-

RMF (Risk Management Framework)
The Risk Management Framework (RMF) from NIST (National Institute of Standards and Technology) is a structured, seven-step process that helps…
-
Compliance Checking (Testing)?
Compliance checking (or compliance testing) is the process of evaluating whether an organization, system, or process adheres to regulations, policies,…

